THE OPERATOR: A Counterintelligence Officer Built the UFO Disclosure Movement. He Never Left the Payroll.
The architecture of managed disclosure, mapped from Wright-Patterson to your social media feed.
SUBJECT: OPERATIONAL ANALYSIS // COUNTERINTELLIGENCE ARCHITECTURE, PROXY NETWORKS, AND NARRATIVE SUPPRESSION IN THE UAP INFORMATION SPACE
DATE: APRIL 6, 2026
CROSS-REF: THE GHOST GENERAL | THE SUPPRESSION GRADIENT | THE GLOMAR CONFIRMATION | CONFIRMED: THE TESS CONTINGENCY
DATA CONFIDENCE: HIGH (primary source documents, on-record government statements, SEC filings, witnessed evidence, corroborated testimony). Where confidence is lower, it is noted explicitly.
There is a version of this story that is comfortable to tell. A patriot inside the Pentagon discovers the government is hiding evidence of non-human intelligence. He resigns in protest. He goes public. He fights for the truth. Congress listens. The walls begin to crack.
It is a good story. It has a hero, a villain, and a ticking clock. It has been told on Joe Rogan, on 60 Minutes, on the History Channel, in the halls of Congress, and in a bestselling book cleared for publication by the same Department of Defense that supposedly tried to silence its author.
We are not going to tell that story.
We are going to tell you what happens when a career counterintelligence officer, confirmed as recently as 2022 to be on the government payroll, builds an information architecture designed to control what you believe about the most extraordinary claim in human history. And we are going to tell you what happens to the people who ask the wrong questions.
THE RÉSUMÉ THEY WANT YOU TO SEE
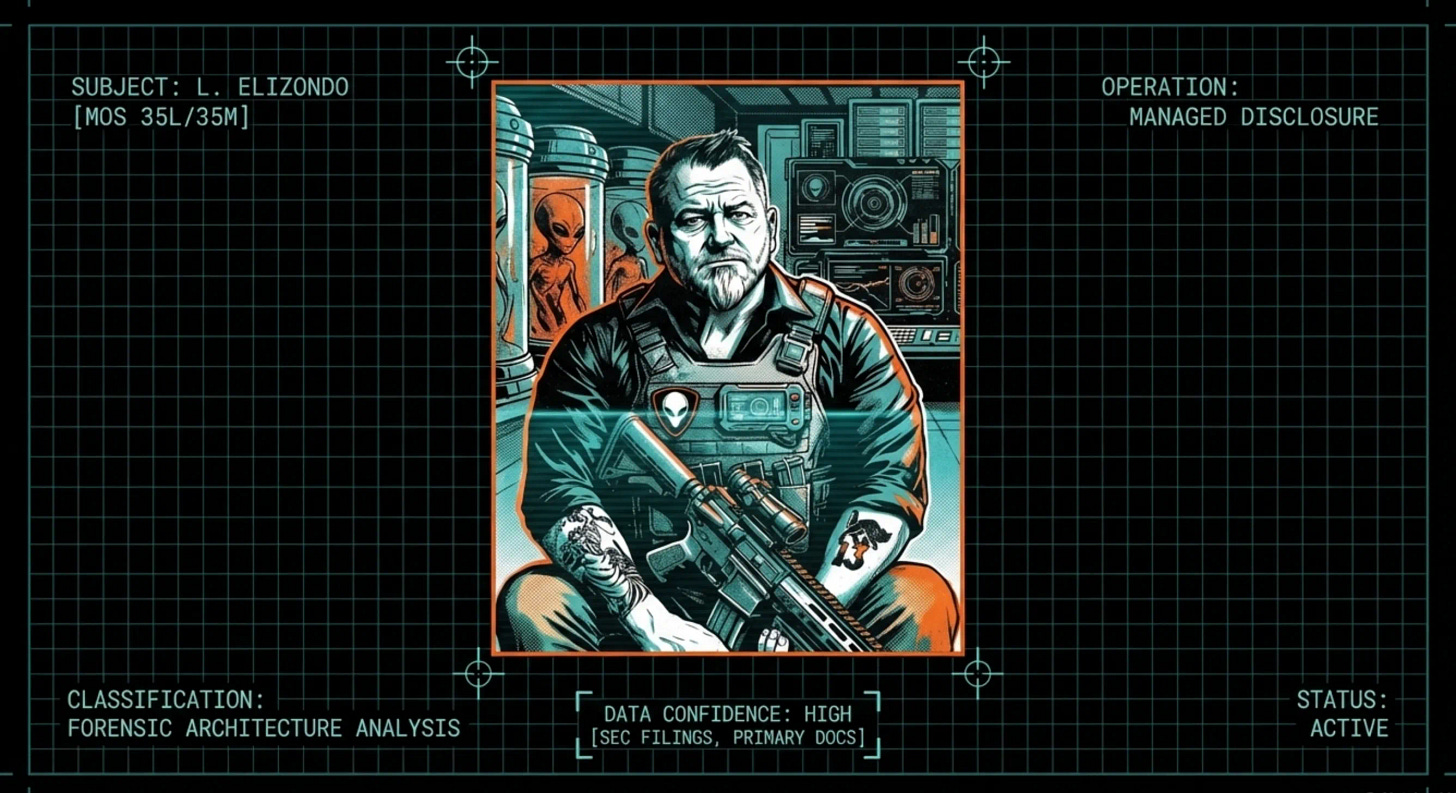
Luis “Lue” Daniel Elizondo enlisted in the United States Army in 1995. He spent two decades as a Counterintelligence Special Agent. The formal designations are MOS 35L and 35M. The informal job description is this: you learn how to identify threats, recruit assets, manage deception operations, run information campaigns, and neutralize anyone who disrupts your mission.
His deployments included Korea, Kuwait, Afghanistan, and South America. He managed classified intelligence operations at Guantanamo Bay’s Camp Seven, the most restricted facility in the detention complex, running missions against al-Qaeda, ISIS, and Hezbollah. His final DoD performance evaluation, dated 2016, praised his ability to manage highly classified programs on a global scale. According to Keith Kloor’s reporting in Issues in Science and Technology, the evaluator noted his office had “identified and neutralized 6 insider threats” and “co-authored 4 national-level policies involving covert action.”
Read that last line again. This is not an analyst. This is not a bureaucrat who stumbled onto UFO files. This is a professional whose government formally evaluated him on his ability to write and execute covert action policy. Covert action, by definition, involves narrative control, plausible deniability, and the manipulation of target populations.
His employer assessed him as excellent at all of these things.
THE SENTINEL ASSESSMENT: Elizondo’s professional background is not incidental to his public role. It is the lens through which every subsequent action must be evaluated. A career counterintelligence officer does not stop being a counterintelligence officer when he resigns. He simply changes his operating environment.
THE THREE RESIGNATIONS
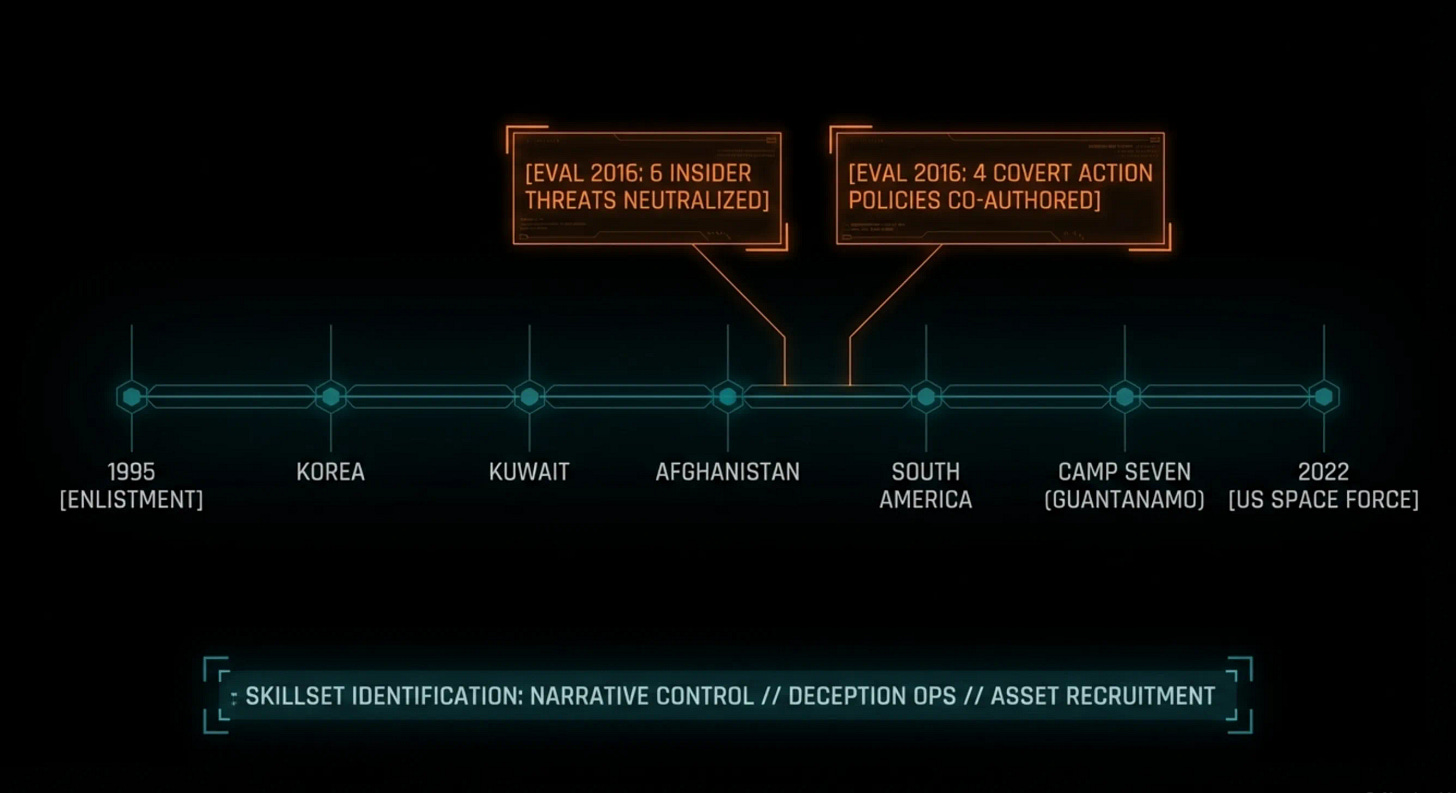
The founding mythology of the modern UFO disclosure movement rests on a single dramatic act: Elizondo’s resignation from the Pentagon on October 4, 2017, accompanied by a letter to Secretary of Defense James Mattis urging him to confront the UAP threat.
The internal record tells a different story. FOIA’d documents obtained by The Black Vault (case 18-F-0324) reveal what actually happened.
On October 3, Elizondo informed his direct supervisor he was leaving for a “fleeting job opportunity that required his immediate availability.” On October 4, the famous Mattis letter appeared, but Elizondo did not hand it in personally. It was delivered to the USDI Chief of Staff’s office by an unnamed third party of “uncertain provenance” after Elizondo had already cleared out of the building. On October 6, Elizondo told a superior by phone that he resigned because the job was “too stressful on his family.”
Three different reasons in three days. The letter that launched a thousand headlines was a planted document, delivered by a ghost, after the author had already left.
But there is a fourth document that reframes the entire sequence. On April 2, 2026, John Greenwald (@theblackvault) of The Black Vault published recovered emails between Elizondo and Brennan McKernan, former director of the UAP Task Force, obtained through lateral FOIA requests on recipients’ mailboxes after the DoD claimed Elizondo’s own emails had been destroyed. Among the 26 pages of correspondence: on September 25, 2017, nine days before the resignation, an email the Navy deemed responsive to this Elizondo-scoped FOIA request was sent to Neill Tipton, a Senior Executive Service official at OUSD Intelligence and Security, with a draft memo titled “AATIP-DDI TCSP.” The email reads: “Per SECDEF’s Front Office guidance to you and me, I took the liberty of drafting a memo at the Unclassified level that helps you better assume the new responsibilities for AATIP.” On October 3, the day before the resignation, Tipton replied that he was reviewing the memo. Elizondo responded: “Perfecto!”
He was not storming out in protest. He was drafting an orderly transition document for his replacement, on instructions from the Secretary of Defense’s front office, and finalizing the handoff the morning before he walked out the door.
Elizondo later confirmed in his memoir that the resignation was coordinated in advance with Jay Stratton, a senior intelligence official at the Office of Naval Intelligence. The plan: Elizondo would go public and drive the media campaign from outside. Stratton would remain inside the government and push the agenda from within.
This is not whistleblowing. This is a planned operation with an outside man and an inside man. In intelligence terminology, it is a covert influence campaign with compartmentalized roles.
THE SENTINEL ASSESSMENT: The discrepancies in Elizondo’s resignation narrative are not minor inconsistencies. They reveal a staged exit designed to create a public mythology. The Mattis letter was not a cry of conscience. It was a press release delivered through a cut-out.
THE WHISTLEBLOWER ON THE PAYROLL
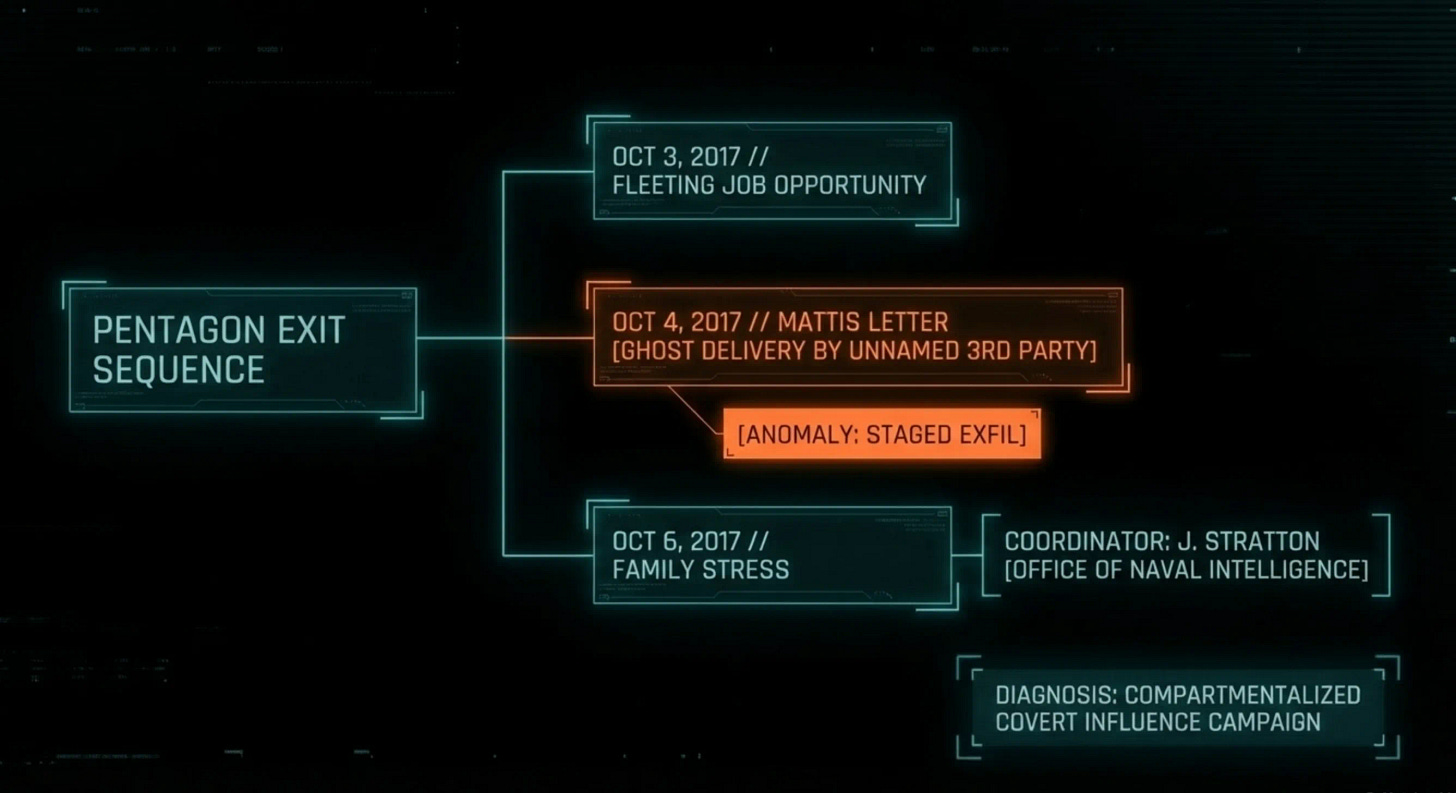
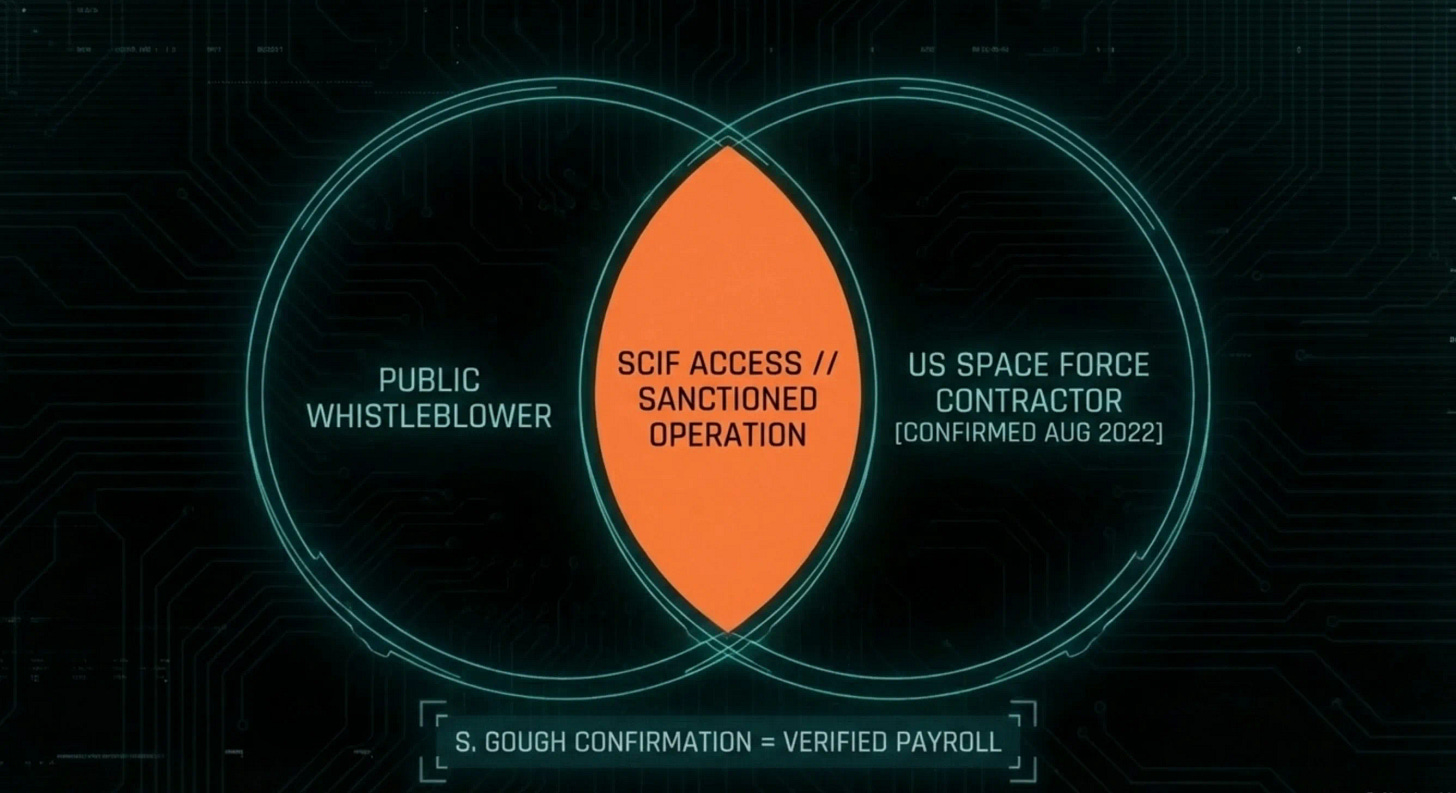
Here is the fact that should end the debate about whether Elizondo is a rogue truth-teller or a sanctioned operator.
In August 2022, Liberation Times reported that Elizondo was employed by the United States Space Force. Pentagon spokesperson Susan Gough officially confirmed the arrangement, stating that Elizondo “provides technical advice on a variety of classified topics.” No termination of this arrangement has been publicly reported.
Let that sink in. Every Rogan appearance. Every congressional briefing. Every media tour for his book. Every impassioned plea for disclosure. All of it occurred while the man was drawing a paycheck from the Department of Defense for classified work.
There is a difference between a whistleblower who retains a clearance and a contractor who draws a paycheck. David Grusch filed through the Inspector General, faced documented retaliation, had his medical records leaked, and fought the system at every step. That is what whistleblowing looks like. Elizondo signed a contract and got paid. While running the most visible public information campaign in UFO history. Those are not the same thing.
The recovered emails documented above tell the same story from a different angle. The DoD destroyed Elizondo’s email archive. The Black Vault recovered portions through lateral FOIA. What they show is not a rogue operator cut off from the institution. It is a man in regular, casual communication with the director of the UAP Task Force, sharing news articles about drone incursions at nuclear sites, coordinating meetings, and exchanging personal cell numbers. The records the DoD said no longer existed were sitting in other people’s inboxes.
The Space Force confirmation also resolves the question of how Elizondo accesses SCIFs to brief Congress. A private citizen cannot walk into a Sensitive Compartmented Information Facility. But a contractor with an active clearance and an ongoing relationship with the defense establishment can. Elizondo’s access to classified spaces is not evidence of his credibility as a whistleblower. It is evidence of his ongoing operational relationship with the institution he claims to be exposing.
THE SENTINEL ASSESSMENT: The Susan Gough confirmation is the single most important fact in the UFO disclosure debate. A government contractor conducting a public information campaign is, by definition, conducting a sanctioned information campaign. Everything Elizondo says in public either has the government’s tacit approval or is a violation of his contract. There is no third option.
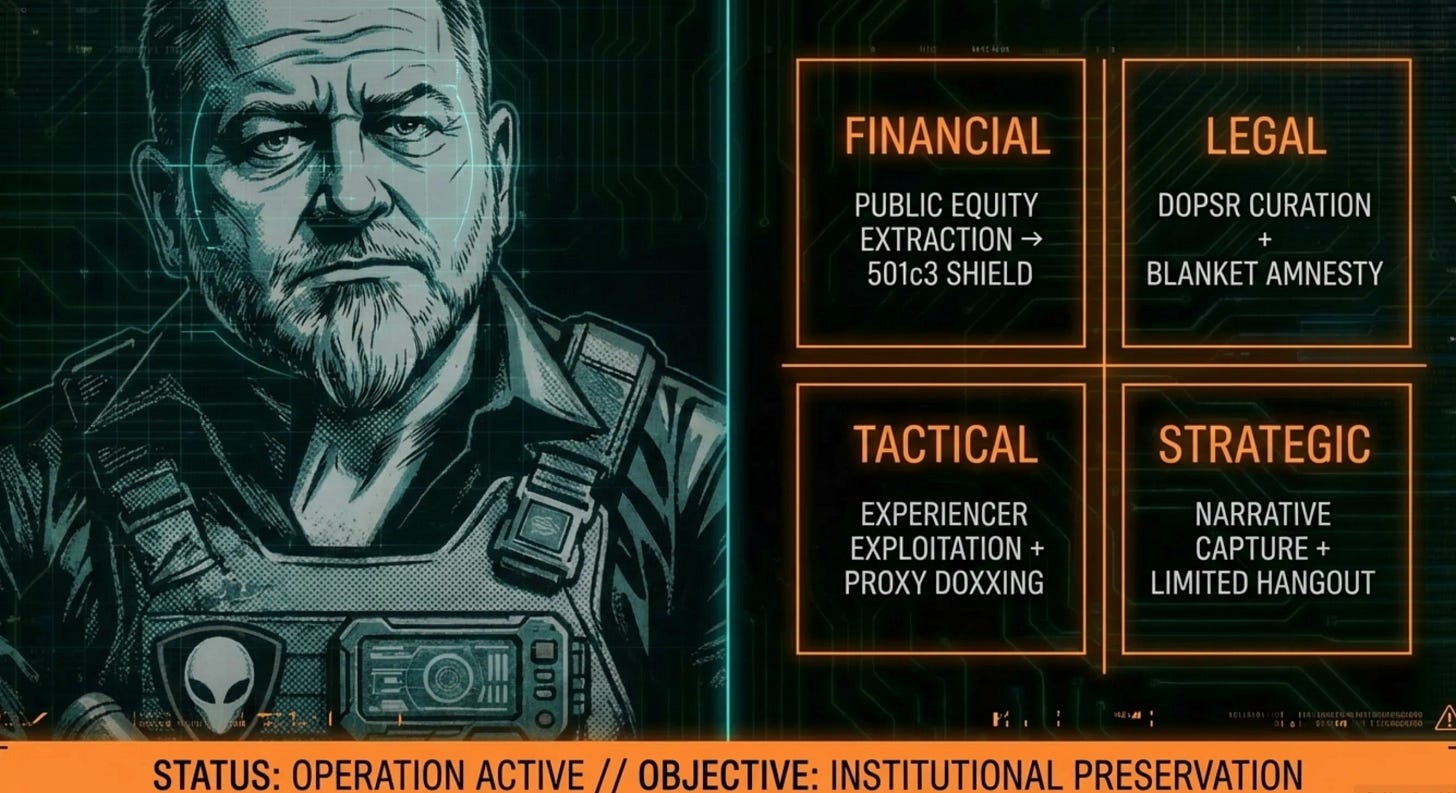
THE MONEY MACHINE
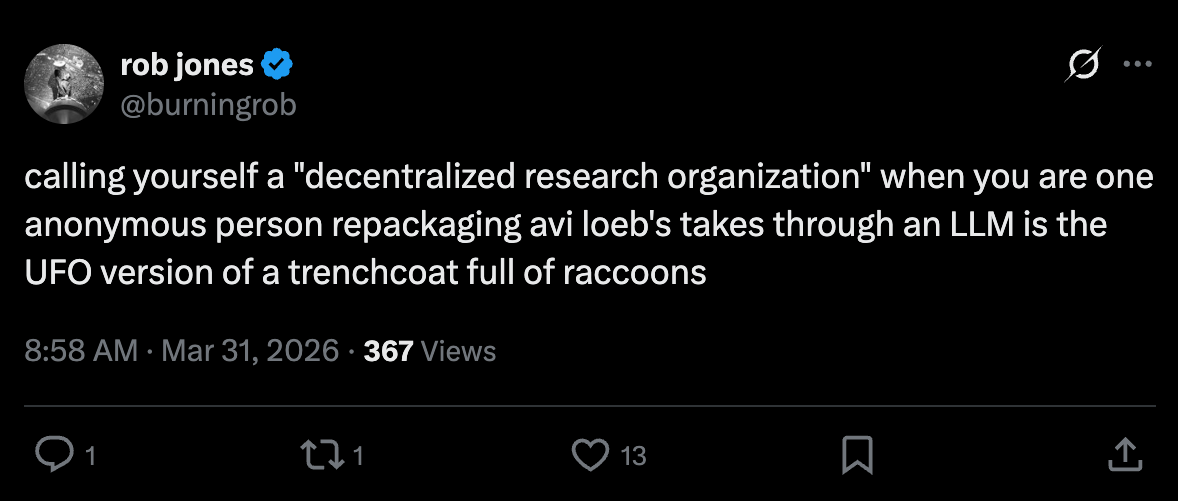
Days after his October 2017 resignation, Elizondo joined To The Stars Academy of Arts and Science (TTSA), a public benefit corporation co-founded by Tom DeLonge of Blink-182. Elizondo assumed the role of Chief of Security and Special Programs. Christopher Mellon, former Deputy Assistant Secretary of Defense for Intelligence, joined alongside him.
TTSA’s SEC filings reveal what this actually was.
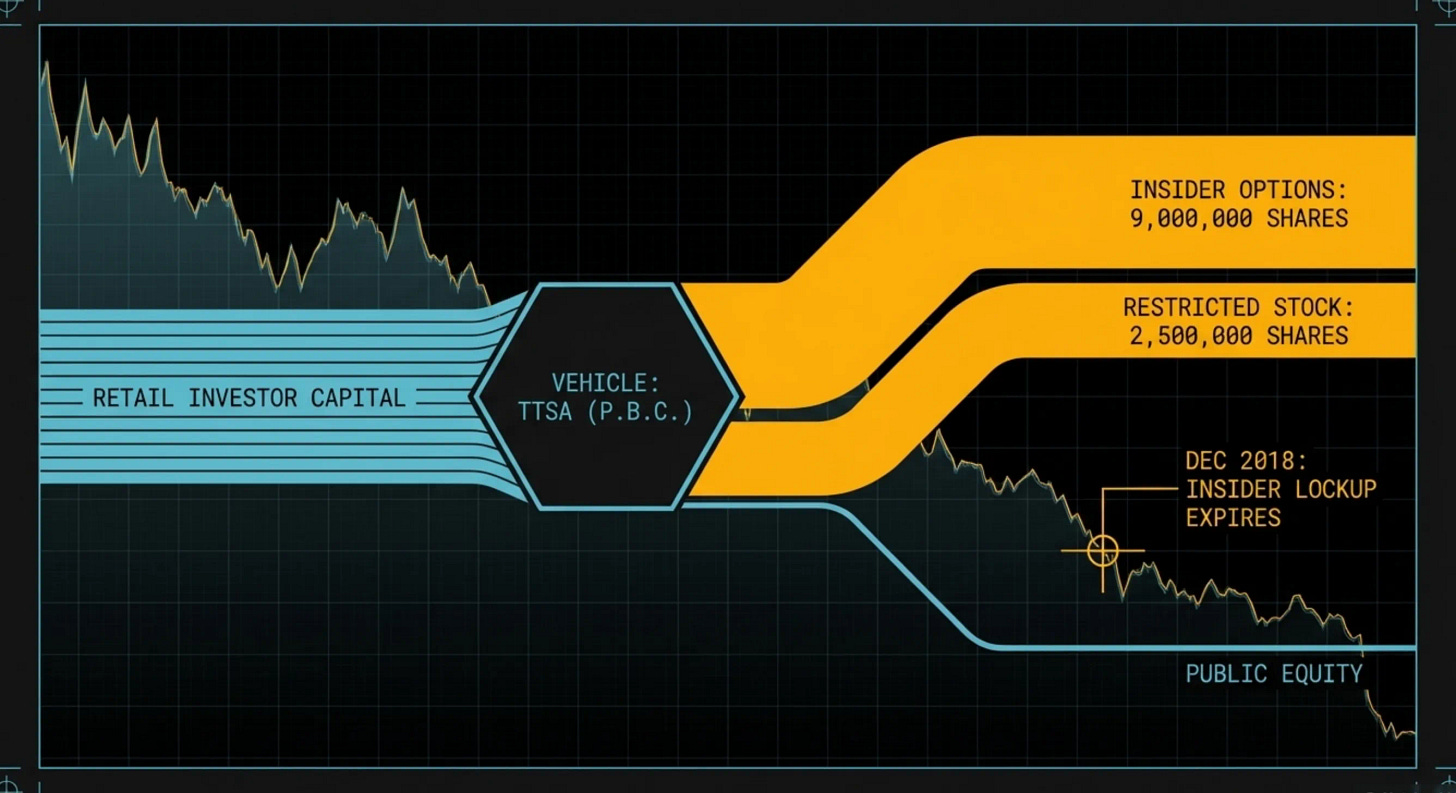
TTSA raised capital through a Regulation A+ offering, a mechanism that allows companies to sell shares directly to non-accredited retail investors without the scrutiny of a traditional IPO. Before that offering ever opened to the public, the company’s officers and directors granted themselves 9,000,000 stock options and 2,500,000 restricted stock units (RSUs), valued at an estimated fair value of nearly $19 million using a Black-Scholes pricing model. This is pre-dilution insider equity. The people running the company awarded themselves the controlling stake before a single outside dollar came in.
Then they opened the offering. Thousands of retail investors, many of them UFO enthusiasts who believed they were funding genuine disclosure, bought shares at the public offering price. The SEC filings warned them, in the fine print, exactly what would happen next: “The ownership percentage of our existing stockholders will be diluted” as insiders exercised their options. Dilution means each new share the insiders convert reduces the proportional value of every share the public holds. The insiders’ equity grows. The retail investors’ equity shrinks. Same pie, more slices for the people who set the terms.
By December 2018, 5,104,167 of those insider options had vested and were exercisable. The retail investors who funded the company had no equivalent liquidity event. The insiders could sell. The public could hold.
The product TTSA actually delivered was not aerospace technology. It was entertainment. Elizondo starred in Unidentified: Inside America’s UFO Investigation on the History Channel, produced through TTSA. The company that raised millions on the promise of scientific research and advanced aerospace engineering used those dollars to produce a television show starring its own Chief of Security. The investors funded the product. The insiders were the product.
Then TTSA pivoted entirely to entertainment content. Elizondo left. Mellon left. Former Lockheed Skunk Works engineer Steve Justice left. The investors got content. The insiders got out.
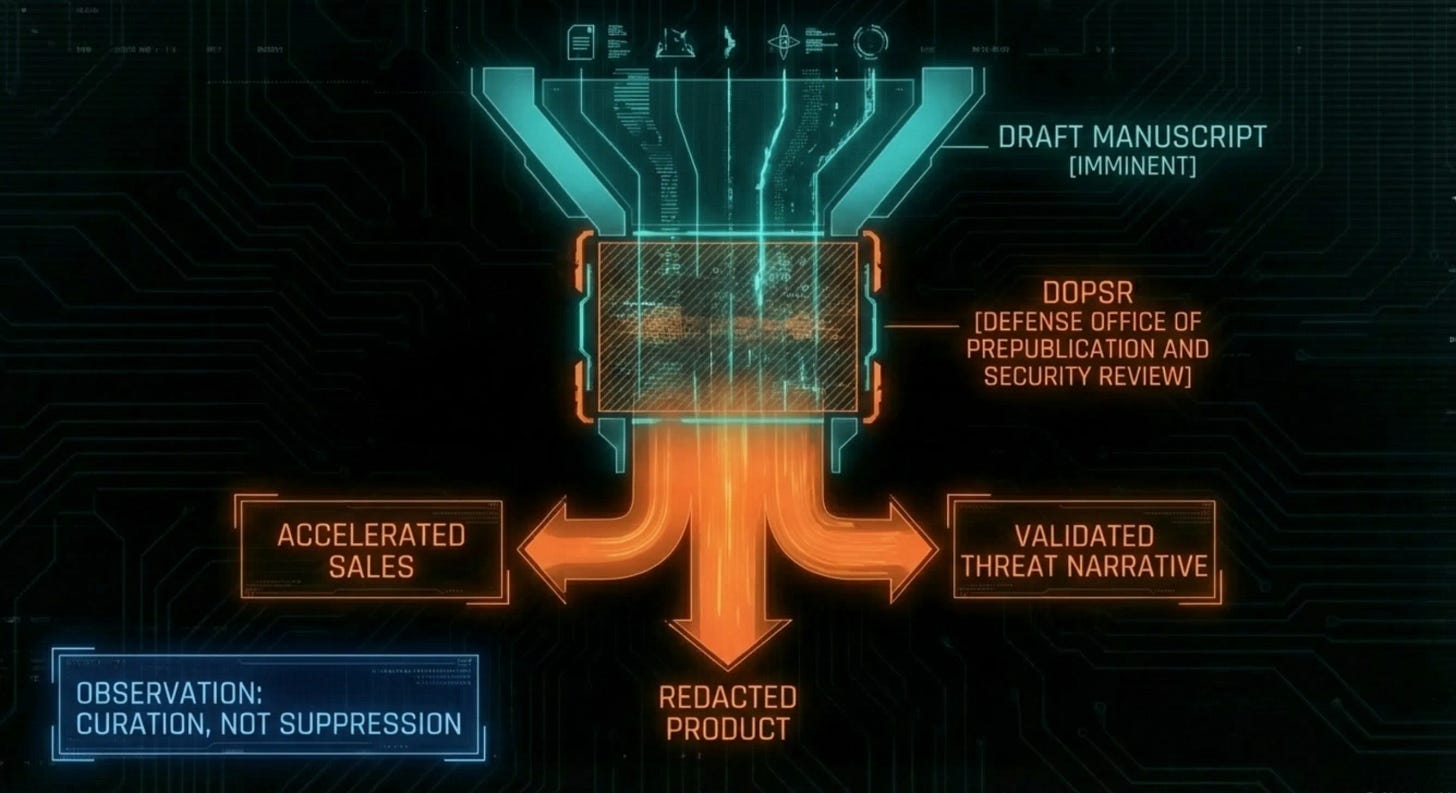
Meanwhile, Elizondo published Imminent through HarperCollins in August 2024. The book went through the Pentagon’s manuscript clearance process, the Defense Office of Prepublication and Security Review (DOPSR). Portions were redacted. Elizondo cites these redactions as proof the government is hiding the truth.
Think about that for a moment.
DOPSR exists to prevent the release of classified information. It has the authority to reject manuscripts entirely. If the Pentagon genuinely wanted to silence Elizondo, they would have killed the book. They did not. They approved a book that accuses the Pentagon of hiding alien technology, complete with dramatic black bars that generate headlines and drive sales.
The redactions do not prove suppression. They prove curation. They tell the reader this man knows secrets without the government ever having to confirm or deny what those secrets are.
THE SENTINEL ASSESSMENT: The financial trail runs from TTSA investor dollars through a corporate pivot to entertainment, into a book deal cleared by the Pentagon’s own review office. At no point does the money flow suggest a grassroots rebellion. It suggests a product line. The investors funded the show. The show sold the book. The book sells the narrative. The narrative sells the policy. And the man at the center of all of it never stopped cashing government checks.
THE AMNESTY PLAY
Elizondo’s most consequential policy advocacy is not disclosure. It is amnesty.
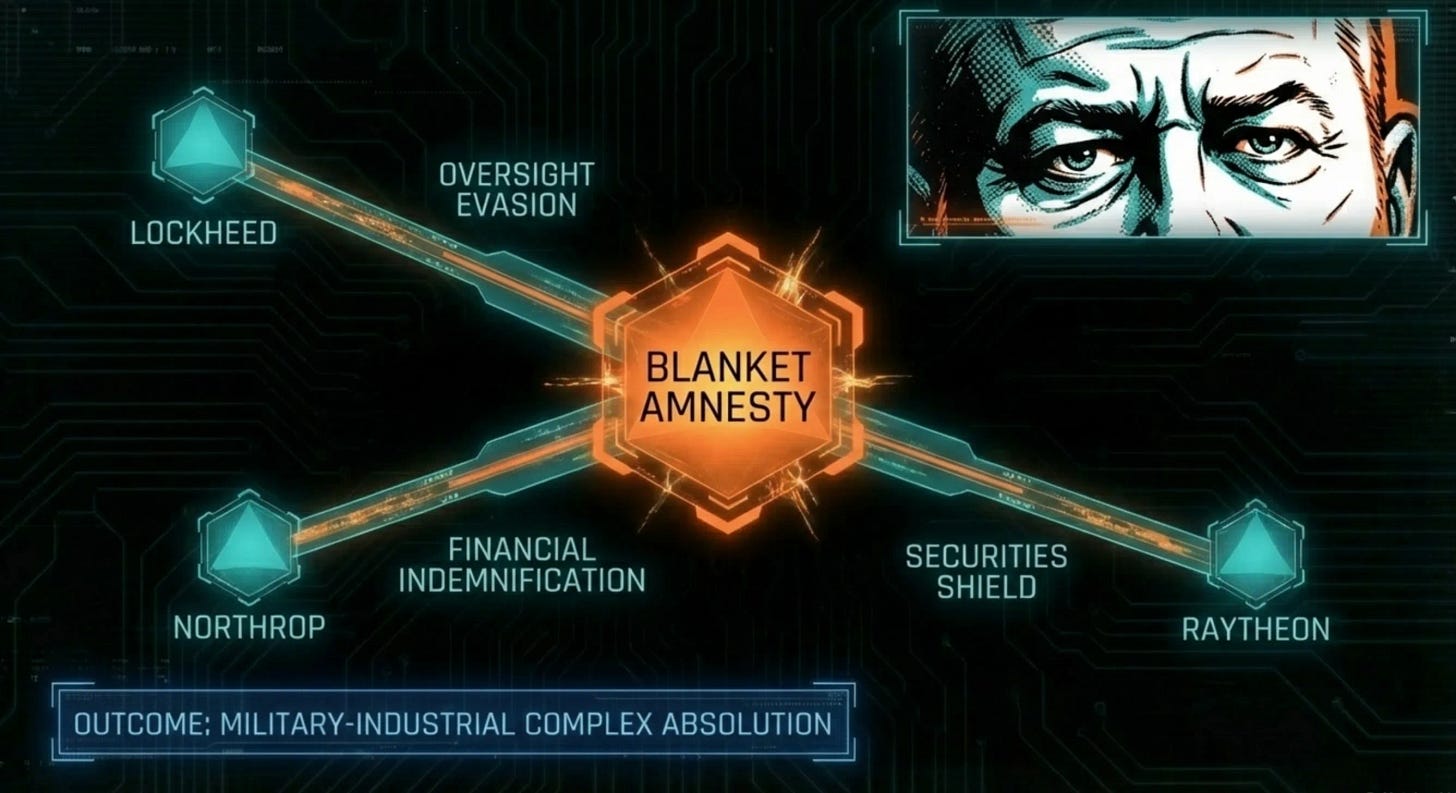
He has repeatedly and publicly championed legal frameworks that would grant immunity to private aerospace defense contractors and mid-level corporate managers who have allegedly been hiding crashed UAP materials and operating reverse-engineering programs outside Congressional oversight for decades.
Think about who benefits from this. Not the public. Not the whistleblowers, who already have legal protections under existing statute. The beneficiaries of blanket amnesty are the defense contractors, the Lockheeds and Northrops and Raytheons, who would be absolved of decades of potential financial misappropriation, securities fraud, and Congressional oversight evasion.
Elizondo frames amnesty as a necessary precondition for truth. The framing is elegant. But the outcome is indemnification of the military-industrial complex, advocated by a man who is on the military’s payroll, laundered through a disclosure narrative that makes the advocacy feel righteous.
THE SENTINEL ASSESSMENT: Follow the money backward from the amnesty push and you arrive at the largest defense contractors on Earth. Follow it forward from TTSA and you arrive at the same place. Elizondo is not positioned between the public and the truth. He is positioned between the defense industry and accountability.
THE HANDLER’S TOOLKIT
What we have described so far, the staged resignation, the ongoing government contract, the financial vehicles, the amnesty play, is the strategic architecture. It operates in daylight, on television, in Congressional hearing rooms.
Now we go underground.
The tactical architecture is uglier. It is built on harassment, doxxing, and the systematic exploitation of psychologically vulnerable people.
Multiple independent researchers who have publicly questioned the Elizondo narrative have been subjected to coordinated digital harassment campaigns. These are not random trolls. The harassment follows a consistent operational pattern: a researcher publishes critical content, and within hours, a network of aggressive accounts descends to attack their credibility, expose their personal information, and in documented cases, threaten physical harm.
Two accounts in particular have been extensively documented: one operating under the handle “King Milk Fart” (KMF) and another under “Sawan.”
When military veteran Beverly Holmes questioned the UAP narrative, KMF doxxed her by posting the name and photograph of her underage son online. He called her a 'crazy bitch.' The Washington Spectator documented this and the broader pattern of cyberstalking in detail.
Former Elizondo ally Jeremy McGowan reported that the network used photographs of his children during targeted attacks after he distanced himself from the group. McGowan had posted a UFO sighting on Reddit that led to him appearing on Elizondo’s History Channel show Unidentified. When he witnessed red flags and stepped back, the network turned on him.
That detail matters. This is not a machine that only targets outsiders. It eats its own.
When journalist Ken Klippenstein published David Grusch’s medical records obtained through standard law enforcement channels, Sawan issued a direct threat: “We are coming after you. You have no idea how fucked you are.”
Sawan described centrist researchers and skeptical journalists as “roaches that need to be exterminated.”
The Washington Spectator documented the cyberstalking in detail. McGowan filed complaints with the Las Vegas Police Department and told the Spectator he was exploring a formal complaint with the FBI’s Internet Crime Complaint Center.
Researchers operating under the pseudonyms Red Panda Koala and Tupacabra, both prominent critics of the Elizondo narrative, have been targeted by doxxing campaigns connected to this same network. Red Panda Koala has detailed these threats in multiple public forums, including a February 2026 appearance on the UAP Unidentified Alien Podcast, where he described the doxxing as being perpetrated by individuals “connected to very high profile figures” in the disclosure movement.
The evidence reviewed by The Sentinel Network goes further. It has names.
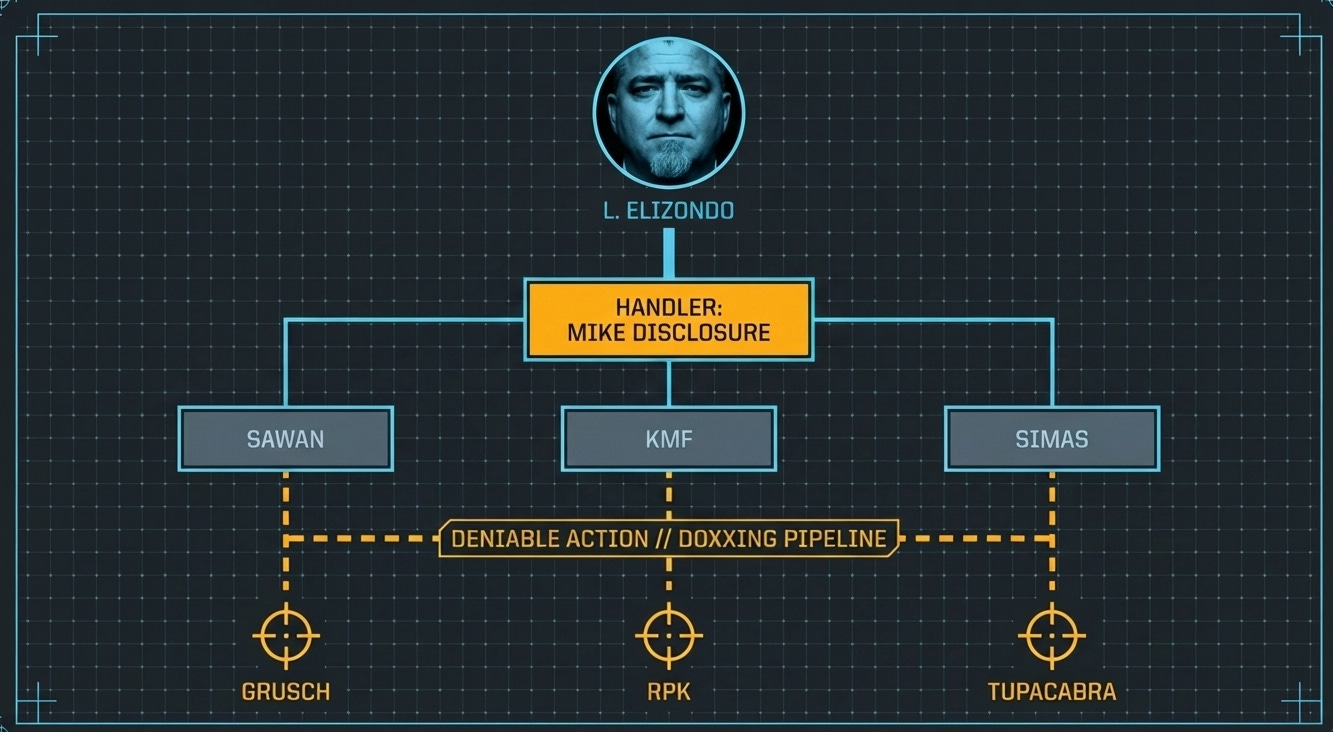
In a public statement on X, Red Panda Koala identified the individual who compiled and distributed doxxing dossiers on him and Tupacabra: an account operating as @MikeDisclosure, described by RPK as a personal friend of Elizondo.
The dossiers were not casual internet research. They contained addresses, phone numbers, ages, dates of birth, height, hair color, eye color, previous addresses, employment history, family member addresses, family member phone numbers, family member ages and dates of birth, current home square footage, and number of beds and baths. That is a professional-grade intelligence product.
Mike Disclosure sent these dossiers to Jon Simas. According to RPK's public account, corroborated by Simas himself in a recorded X Spaces conversation, Simas was experiencing a mental health crisis at the time and had been involuntarily committed less than a week prior. Mike Disclosure was aware of this. He sent the dossiers anyway. He then suggested Simas use the information to make RPK and Tupacabra "face consequences irl."
Simas did not ask for this information. It was pushed to him, unsolicited, by someone who knew he was in crisis.
That is the mechanism. You do not tell the asset to attack. You hand a loaded weapon to someone you know is unstable and you suggest the target deserves consequences. The handler’s hands stay clean. The mentally unwell person takes the fall.
In the public X Spaces conversation, where Simas described receiving the dossiers unsolicited, he offered two theories for why Mike Disclosure sent them: either Mike hoped Simas would publish the home addresses and doxx RPK and Tupacabra directly, or Mike was counting on the fact that Simas, who was open about his mental health struggles, might physically show up at their homes. Simas called it “evil.” He said Mike Disclosure “didn’t know my integrity” and “didn’t know that I would never fucking do that in a million years.”
The recipient is on record saying he was weaponized. The handler picked him because he was in crisis. And the handler’s proximity to Elizondo is not in dispute.
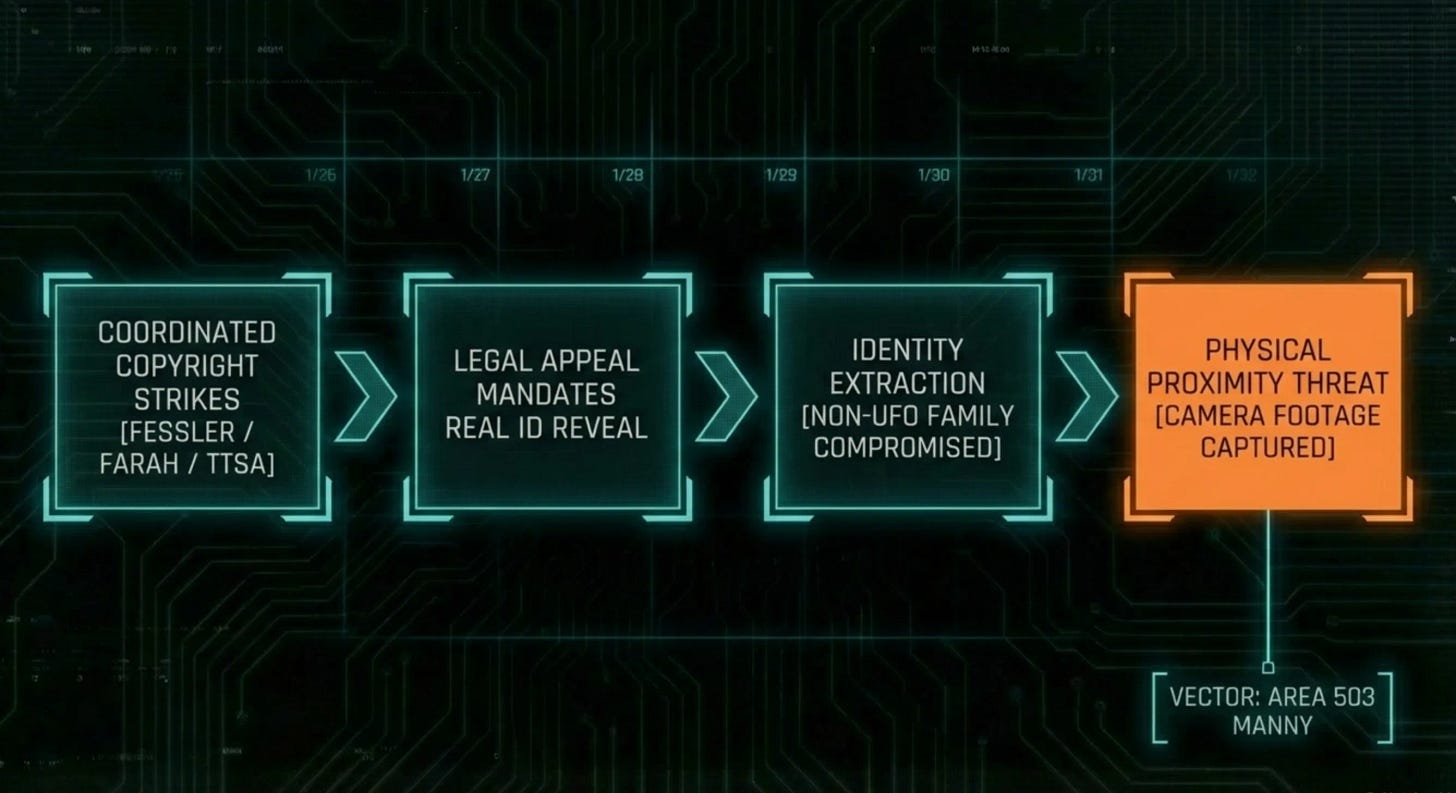
The network also weaponized copyright law as a doxxing tool. UFO documentary filmmaker Area 503 Manny produced a critical documentary titled “Who’s Lue?” The network filed a false copyright strikes against his work. These were not random complaints. They were coordinated. Thomas Fessler, host of the Disclosure Tonight podcast and a close Elizondo associate, filed the first strike. According to Manny’s public account, Fessler then enlisted Dan Farah, Elizondo’s talent agent and producer of Age of Disclosure, to use his contacts at the History Channel to file a second. Tom DeLonge’s To The Stars Academy filed a third. Three strikes from three different entities in the Elizondo orbit, timed to hit simultaneously, designed to permanently ban Manny from YouTube.
When Manny appealed the strikes, the legal process required him to submit his real name and address. Within a week, Thomas Fessler was reading Manny's legal name on air. Then someone physically showed up at his mother's house asking questions about him. In a recorded X Spaces conversation, Manny stated they obtained the address from the copyright appeal process. There is security camera footage. People credited in the documentary, including researcher Rich Gouffon, were also targeted by the harassment network after the film's release.
Read that again. They filed a false copyright claim specifically to force the target to reveal his identity through the appeals process. The legal system itself became the doxxing mechanism.
The network's technical capabilities extend further. According to a written statement published by Red Panda Koala from a former operative who infiltrated the harassment network, members would befriend targets online, offer to share "inside information," then send links via email or messenger containing malware that allowed the sender to infiltrate the victim's device and harvest personal information. Victims had no idea they were compromised until the information was weaponized against them. If accurate, this constitutes a violation of the Computer Fraud and Abuse Act. The Sentinel Network has not independently verified this claim but notes it is consistent with the professional-grade dossier contents documented.
The hate was also unleashed on Garry Voorhis, one of the actual witnesses to the 2004 Nimitz Tic Tac event. A military veteran who was there for the encounter the entire disclosure movement is built on, targeted by the movement that claims to fight for people like him.
Jay Anderson, host of the Project Unity podcast, took these allegations to the largest possible platform in December 2025, appearing on The Joe Rogan Experience (Episode #2430). Anderson described Elizondo’s pattern of cultivating aggressive fans as a deliberate control mechanism, naming the harassment network and identifying Red Panda Koala and Tupacabra as specific targets. Joe Rogan’s response when Anderson described Elizondo’s tactics: “He’s also one of the guys calling for amnesty?”
The pattern extends beyond critics. It was deployed against David Grusch, the most significant UAP whistleblower in a generation.
In a recorded X Spaces conversation, former Disclosure Tonight contributor Sawan confirmed on the record that Mike Disclosure pushed him to publicly attack Grusch. Mike messaged Sawan daily asking “are you working on this?” When asked why he chose Sawan specifically, Mike Disclosure told x user LM: “Of course I would pick him, because if this goes sideways, it’s going to be on him.” Sawan was selected as the expendable cutout because of his volatile posting history. He was the deniable weapon.
A second witness, speaking publicly as LM, went further. He stated he was in direct conversations with Elizondo where Mike Disclosure was also present. That the information Mike used to run operations came directly from Elizondo. That Mike asked multiple people, including LM’s wife who had access to law enforcement databases, to illegally pull Grusch’s medical records. LM refused. He stated Elizondo was “still actively” feeding information to Mike Disclosure at the time of the testimony.
This is no longer a question of overzealous fans. These are public statements from multiple named witnesses placing Elizondo in the same conversations as the man who orchestrated the targeting of a federal whistleblower. The information pipeline ran through Elizondo. Mike Disclosure was the operational cutout. Sawan was the expendable tip of the spear.
The scale of the coordinated network is larger than any single handler. John Greenwald (@theblackvault), founder of The Black Vault, has confirmed that an infiltrator reported private Facebook groups of roughly 300 people coordinating targeted attacks as early as 2019. Someone infiltrated one of these groups and was able to predict specific attacks before they happened, including a fabricated racism accusation against Greenwald using his own Halloween decorations. Three hundred people. Coordinated targeting. Predetermined narratives. That is not fandom. That is infrastructure.
Elizondo was among the first to follow many of these proxy accounts on social media. When the accounts were banned and reconstituted under new handles, Elizondo was among the first to re-follow them. You do not race to reconnect with a random troll’s new burner account. You race to reconnect with an asset you need to maintain contact with.
THE SENTINEL ASSESSMENT: The proxy harassment network is not organic fandom toxicity. It is a compartmentalized suppression operation consistent with the counterintelligence tradecraft Elizondo spent twenty years mastering. The strategic layer (media, Congress, books) stays clean. The tactical layer (doxxing, threats, harassment) stays deniable. The psychologically vulnerable individuals caught in between are exploited twice: once as weapons, once as scapegoats when the harassment is traced.
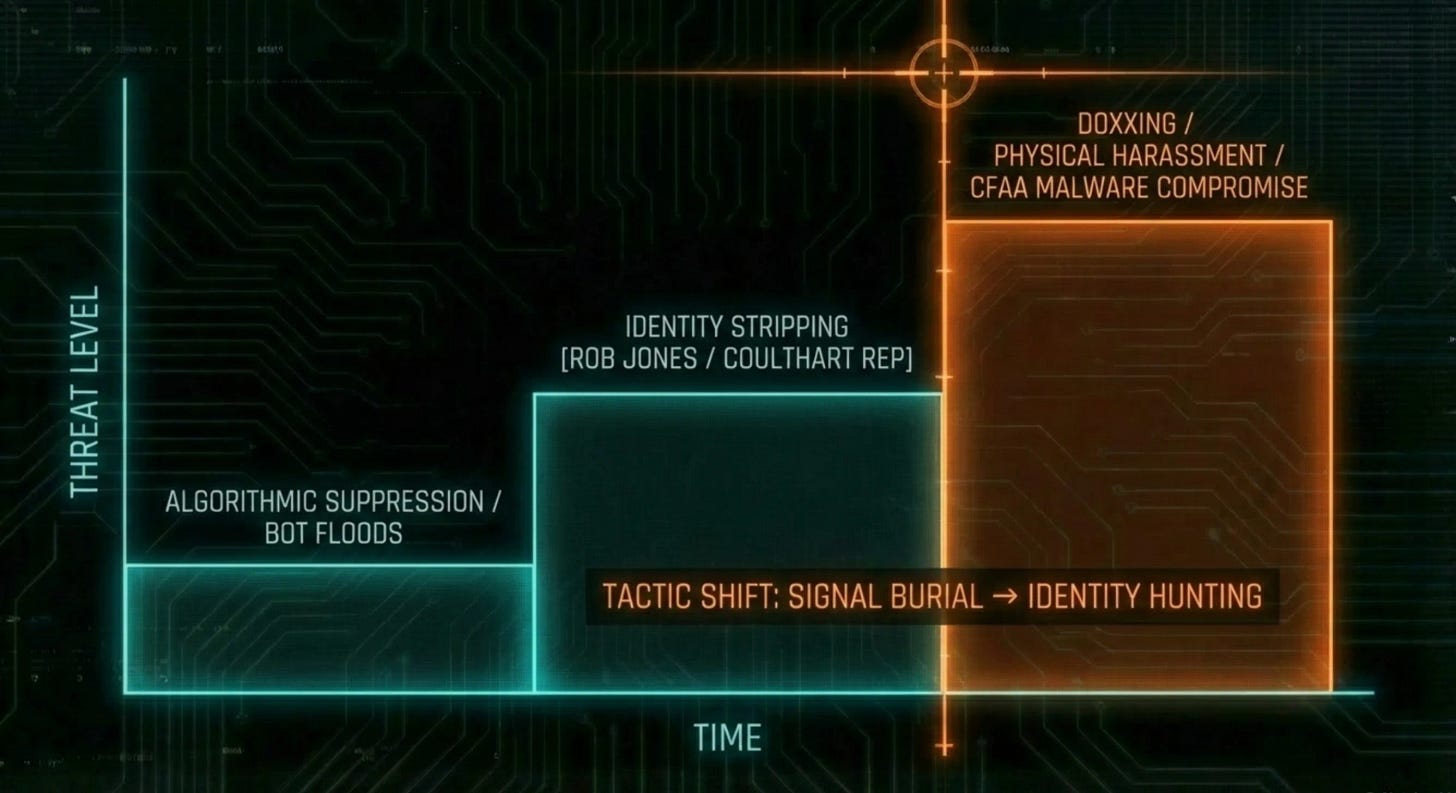
THE SUPPRESSION GRADIENT
We know this playbook because we have lived it.
Since December 2025, The Sentinel Network's coverage of 3I/ATLAS has been met with a coordinated suppression campaign we documented in real time in our February 2026 briefing, THE SUPPRESSION GRADIENT. When we launched THE ATTRITION, the tactic changed. Rather than suppress, the operation flooded our account with over 5,000 bot followers, inflating our engagement with fake accounts that would unfollow when 3I/ATLAS content was posted. Suppression through amplification: poison the metrics, make the publication look artificially boosted, and give platforms a reason to flag the account as inauthentic.
The tactics are structurally identical to those deployed against Red Panda Koala, Beverly Holmes, and Ken Klippenstein.
Bot-pattern comment floods arriving within minutes of publication. Not engaging with the data. Attacking the act of posting. Coordinated downvote brigades designed to prevent algorithmic surfacing. Silent post removals across multiple subreddits with no rule citations. Outright bans, including from r/3i_atlas, r/highstrangeness and r/ufob - many with no explanation and no reply to our appeal.
The operation escalated beyond platform suppression.
We received fabricated documents designed to contaminate our evidence chain. If we published them, our credibility dies. If we referenced them, they could be revealed as fakes to discredit us retroactively. A random internet troll does not send fabricated source documents to an investigative publication. That is an operation designed by someone who understands how journalists work and how to compromise an evidence pipeline.
Reports were filed with Reddit administrators characterizing our publication as a bot operation. Separate reports were filed with the same administrators expressing concern about our mental health.
These are not organic responses to journalism.
Reporting a publication as a bot weaponizes the platform’s own moderation system as a proxy enforcer. Reporting a journalist’s mental health to a platform is the same methodology used when David Grusch’s psychiatric history was leaked to discredit his testimony. Tupacabra’s documentary “Who Doxxed David Grusch?” traces the chain of custody on that leak. Same playbook. Different target.
Then the operation shifted.
For weeks, the bot-pattern accounts had argued the data. They lost. Our analysis held. The orbital mechanics held. The anomalies held. So they stopped arguing the data entirely. We documented a week of silence. Reddit users noticed. No bot replies. Nothing. Then they came back with a new mission.
They stopped attacking what we publish. They started hunting who we are.
The comments shifted from “this is garbage science” to “don’t you wonder who’s behind this?” Accounts began pointing to The Sentinel Network LLC listed on our website, framing it as suspicious: “Who’s getting all the money for this?” Others flooded threads demanding to know our real identities. “Who are these people?” “Are they a psyop?” “Is this an AI agent?” The rhetorical structure rotated. The objective did not. Every comment is engineered to accomplish one thing: strip our anonymity.
Then the same language showed up from a very different source.
Ross Coulthart’s NewsNation platform has served as the primary media amplifier for the Elizondo narrative. Coulthart conducted Elizondo’s highest-profile special report, broke the David Grusch story as a NewsNation exclusive, and the two appear together as a recurring pair on the network. NewsNation describes Elizondo as “quite possibly the most important voice in the modern UFO movement.”
In the weeks prior to this briefing, NewsNation and Coulthart’s “Reality Check” broadcasted stories that The Sentinel Network broke, without attribution. We sent a professional attribution request. Four days later, Rob Jones, the verified Research Producer for Coulthart’s show, posted publicly on X: calling The Sentinel Network “one anonymous person repackaging avi loeb’s takes through an LLM” and “the UFO version of a trenchcoat full of raccoons.”
That is not criticism. That is retaliation. And it connects the amplification layer of the architecture directly to the suppression layer. The people who lift your reporting and the people who attack your identity are the same people. Working for the same network. On the same timeline.
This is the most important escalation to understand because it reveals the transition point in the suppression playbook. Phase one is content suppression: remove the posts, bury the signal, exhaust the messenger. When that fails because the audience grows faster than the bots can suppress, the operation moves to phase two: identity exposure. You cannot silence the message, so you unmask the messenger. Once the messenger is identified, the full toolkit activates. The doxxing. The threats. The reports to employers. The photographs of family members posted online. The mentally unstable proxies pointed at a real name and a real address.
We have watched this exact escalation pattern play out against every critic documented in this piece. Red Panda Koala operated pseudonymously. They unmasked him and doxxed his family. Beverly Holmes questioned the narrative openly. They doxxed her underage son. Jeremy McGowan left the network. They weaponized photographs of his children. Area 503 Manny made a critical documentary. They used the copyright appeals process to extract his real identity, then someone showed up at his mother’s house. The pattern is consistent. The only variable is how long the target can maintain anonymity before the operation breaks through.
We are publishing this because the suppression campaign against The Sentinel Network is not a separate story from the one you are reading. It is the same story. The same architecture. The same playbook. The same escalation pattern. The only difference is that we recognized the pattern because we had already mapped it in the behavior of the Elizondo proxy network before it was turned on us.
THE SENTINEL ASSESSMENT: When the attacks shift from “your data is wrong” to “who are you,” the operation has acknowledged it cannot win on the evidence. Identity exposure is not curiosity. It is targeting. It is the prerequisite step to everything that follows in the handler’s toolkit. We document this not as a complaint but as a data point. The suppression architecture is identical across targets. The only variable is which phase of the playbook has been activated.
THE EXPERIENCER PIPELINE
There is a reason the proxy network recruits from the UFO community and not from, say, political operatives or paid trolls.
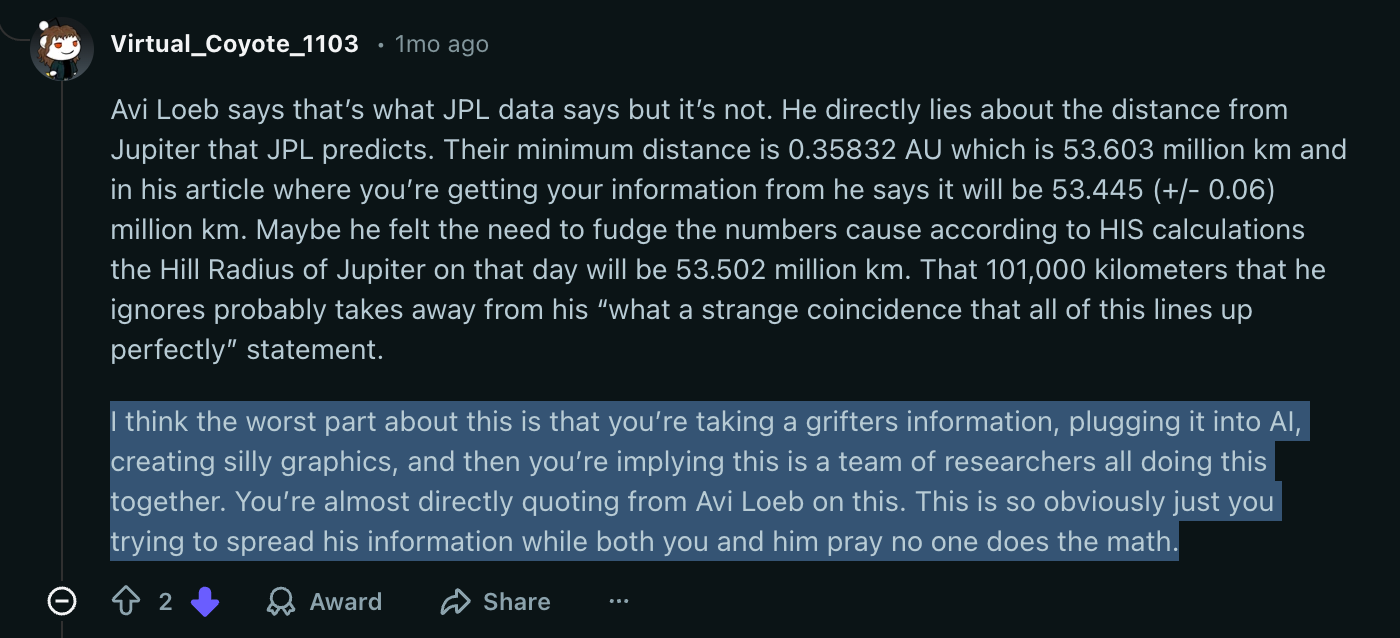
Academic and clinical research has mapped what makes experiencers different, French et al. (2008). Not broken. Not delusional. Different. They score exceptionally high on four traits that, in any other context, would be unremarkable cognitive variations. In a counterintelligence context, they are a recruitment goldmine.
The first is fantasy proneness. A deep, lifelong involvement in a rich imaginative life. These are people whose inner world is as vivid as the outer one.
The second is absorption. The tendency to become so completely engrossed in an experience that everything else disappears. When they focus, they focus totally.
The third is dissociativity. The capacity to detach from immediate reality. To compartmentalize. To separate what they are doing from who they believe themselves to be.
The fourth is the one that matters most: susceptibility to false memories. Research in cognitive psychology has shown that these individuals are significantly more likely to absorb suggested details into their own memory and then defend those memories with absolute conviction. They don’t know the memory is planted. It feels as real as breakfast.
Now imagine you are an intelligence officer and you have identified a community full of people with these exact traits. People who had a profound experience they cannot explain. People who have been ridiculed for it their entire lives. People who are desperate for someone in authority to say: what happened to you was real.
You say those words. You validate them. And they are yours.
Multiple figures within the Elizondo network are self-identified experiencers, including Garry Nolan, who claims childhood encounters, and Chris Bledsoe, who has been studied by NASA and intelligence officials. The question that has not been asked publicly until now: are the individuals doing the doxxing and harassment also experiencers? Are they acting out of cultivated loyalty to a narrative that validates their most profound personal experiences? And if so, who cultivated them?
The Bledsoe case illustrates the pipeline at its most predatory. Jonathan Davies, a UK-based figure, served as a liaison for Bledsoe's "faith healings." In a recorded conversation on X, a father described the process: Davies would identify vulnerable people in the UFO community, people with sick family members, people in crisis. He would tell them Bledsoe could heal them through contact with an entity called "the Lady." The targets were asked to send a photograph of their eyes, a lock of hair, and an item of clothing. DNA. A photograph. Personal effects. Delivered voluntarily by desperate people to a network that was simultaneously running doxxing operations.
One father whose daughter had a rare and severe form of diabetes sent these items after Davies told him Bledsoe had cured someone’s cancer. Nothing happened. His daughter’s condition worsened. He sought real medical help. But the network had his daughter’s biological material, his home address, and his emotional investment.
Christopher Gray, another figure in this same network who was close to Davies and deeply embedded in the Bledsoe belief system, murdered his father in February 2021 while referencing “the Lady” on a live recording. He emailed a confession and the video to a mass distribution list that included many of the most prominent figures in the UFO disclosure movement. UFO researcher Steven Cambian contacted recipients for comment. None would speak on the record. People who attempted to discuss the murder publicly were harassed and threatened. The story was framed as “bad for disclosure.”
That is the endpoint of the experiencer pipeline. A psychologically vulnerable person, absorbed into a narrative framework involving cosmic entities and chosen-one mythology, was used as a harassment proxy until he deteriorated past the point of function. He killed someone. The network closed ranks.
THE SENTINEL ASSESSMENT: The experiencer pipeline is the most operationally elegant element of the architecture. It produces assets who are self-motivated, emotionally invested, and impossible to deprogram through rational argument, because their loyalty is not rational. It is experiential. A counterintelligence officer who understood this dynamic could build an army of true believers who would never need to be paid, never need to be instructed, and never trace back to a handler.
THE GHOST IN THE MACHINE
If you have been reading The Sentinel Network, you already know the name William McCasland.
We profiled him in THE GHOST GENERAL. Major General McCasland commanded the Air Force Research Laboratory at Wright-Patterson Air Force Base, the historic epicenter of American UFO investigations since the 1940s, from 2011 to 2013. After retirement, he joined Applied Technology Associates and the Board of Trustees at Riverside Research, a national security nonprofit serving the DoD and Intelligence Community.
In January 2016, Tom DeLonge emailed John Podesta, Hillary Clinton’s campaign chairman, and named McCasland explicitly. DeLonge wrote that McCasland was “in charge of all of the stuff” at Wright-Patterson, that he “not only knows what I’m trying to achieve, he helped assemble my advisory team,” and that he was “a very important man.” The WikiLeaks archive confirms that McCasland’s wife accepted an invitation to a DeLonge/Podesta meeting.
This establishes the chain of custody for the modern disclosure movement: McCasland, operating at the institutional level, fed DeLonge into the pipeline. DeLonge created TTSA. TTSA became Elizondo’s launch platform. The architecture traces from a two-star general commanding classified aerospace research at Wright-Patterson, through a rock star who was described in leaked emails as a “useful idiot” for military PR, to a counterintelligence officer now running a public information campaign while on the Space Force payroll.
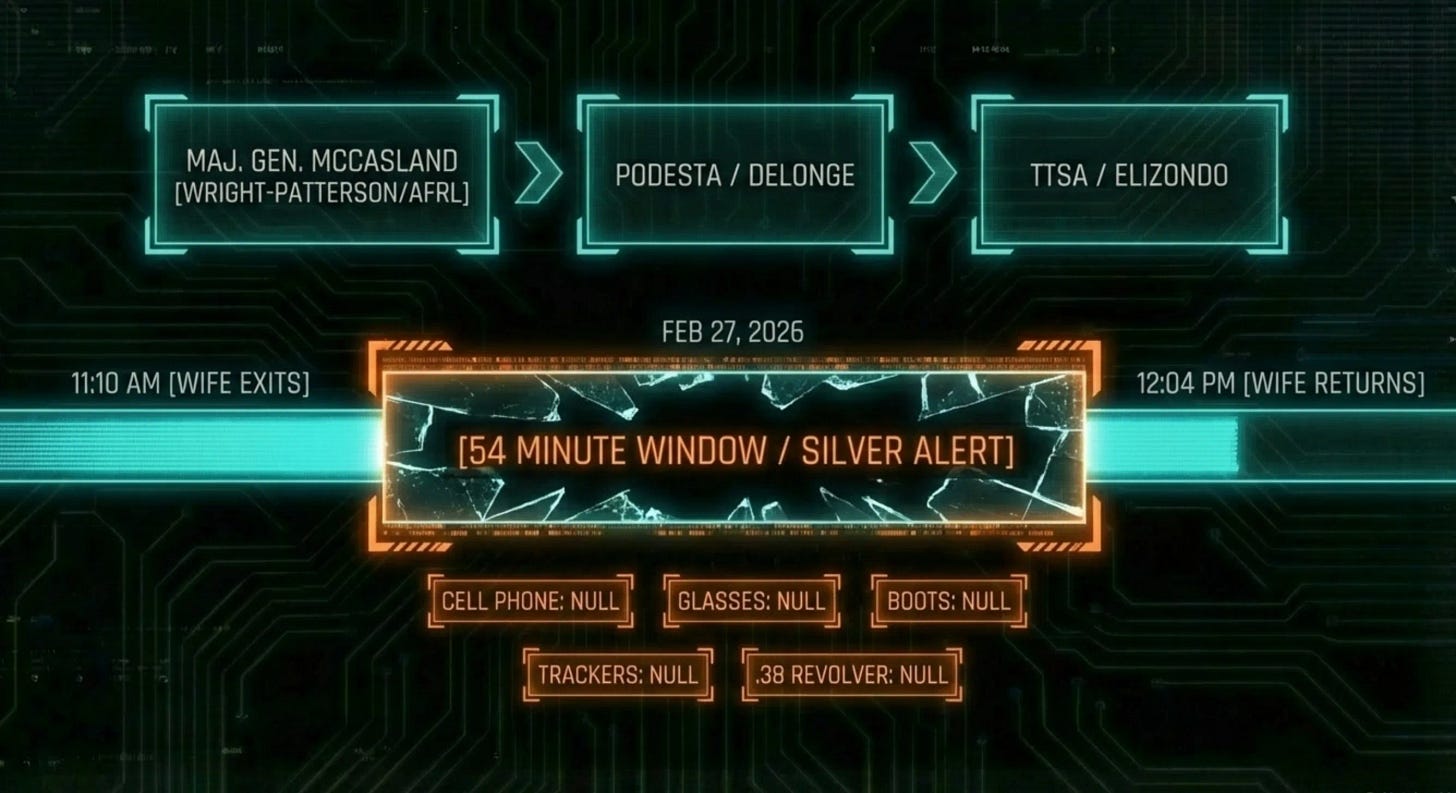
On February 27, 2026, McCasland interacted normally with a repairman at his Albuquerque home at approximately 10:00 a.m. His wife left for a medical appointment at 11:10 a.m. When she returned at 12:04 p.m., he was gone.
A 54-minute window.
He left behind his cell phone. His prescription glasses. All wearable tracking devices.
His hiking boots were missing. His wallet was missing. A .38-caliber revolver was missing.
The Bernalillo County Sheriff’s Office claimed they issued a Silver Alert that we could not locate in the databases. The FBI’s Albuquerque Field Office joined the search. Helicopter infrared sweeps. K-9 units. Drones. Over 700 homes canvassed. No physical trace of the Major General has been located.
He had reported experiencing “mental fog” before his disappearance. Investigators emphasized he remained “arguably the most intelligent person in the room.”
He has not been found.
Elizondo’s public response was immediate and revealing. “I hope and pray this is not one of those cases where a former senior military officer was specifically targeted,” he told CNN, unprompted. A trained counterintelligence officer does not speculate idly. He was introducing a narrative frame before anyone else could set one.
McCasland’s disappearance sits at the intersection of two investigative threads this publication has been documenting for months. THE ATTRITION tracks a pattern of deaths and disappearances among researchers connected to defense aerospace institutions. The piece you are reading now tracks the information architecture that controls the disclosure narrative. McCasland is the node where both threads converge.
We are not asserting causation. We are documenting the pattern. We are noting that the man who helped build the pipeline disappeared four weeks ago and that the man at the other end of the pipeline immediately moved to control the narrative around that disappearance.
THE SENTINEL ASSESSMENT: The McCasland disappearance does not confirm a conspiracy. It confirms a connection. The same institutions, the same individuals, and the same information control dynamics that define the disclosure operation also define the ATTRITION pattern. Whether that convergence is coincidental or structural is the question this publication will continue to investigate.
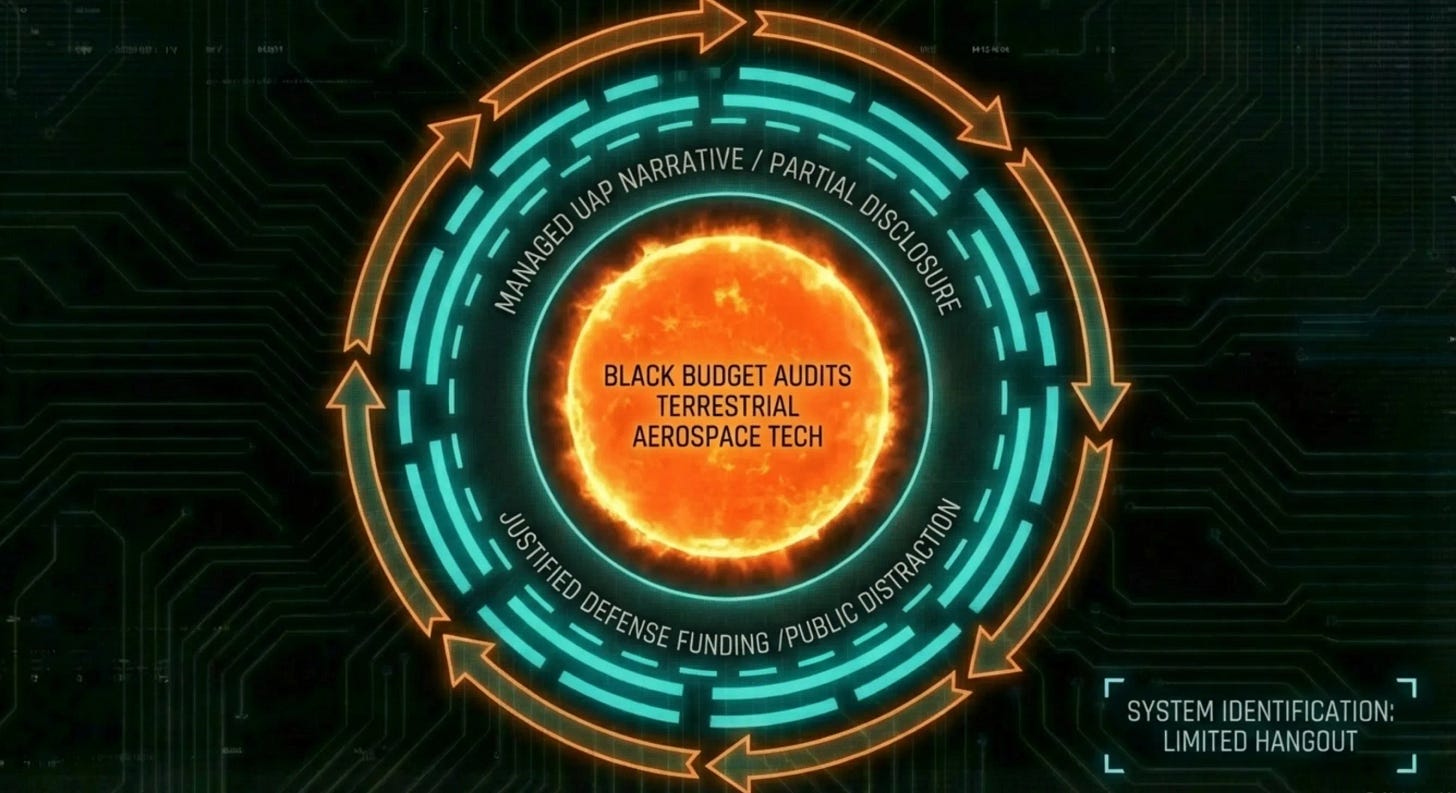
THE LIMITED HANGOUT
In intelligence terminology, a “limited hangout” is what happens when secrecy fails. Rather than deny everything and lose all credibility, the agency admits a fraction of the truth, enough to satisfy public curiosity, while fiercely protecting the core secret. The partial admission becomes the story. The real story stays buried.
Critics have long argued that the entire Elizondo-led disclosure movement is a massive, DoD-sanctioned limited hangout. The logic is straightforward.
By feeding the public videos of anomalous aerial vehicles and encouraging speculation about aliens, the intelligence apparatus accomplishes several objectives simultaneously.
It deflects attention from classified terrestrial aerospace testing.
It creates a threat narrative that justifies increased funding for space-based defense and surveillance systems.
It masks black-budget financial auditing failures that would otherwise attract Congressional scrutiny.
And it provides a controlled channel for public fascination with the unknown. A channel managed by a trained operative on the government payroll, with a book cleared by the government’s own review office, advocating for amnesty that would protect the government’s own contractors.
Every element of the architecture serves the institution, not the public. The videos are real, but their interpretation is managed. The Congressional briefings happen, but in classified spaces where debunkers cannot follow. The book exists, but it was approved by the same Pentagon that supposedly tried to suppress it. The man they call a whistleblower exists, but he never stopped cashing government checks.
This is not disclosure. This is a product.
THE SENTINEL ASSESSMENT: The question is not whether UFOs are real. The question is whether the people telling you about UFOs are telling you the truth about why they are telling you. When every element of a disclosure movement traces back to the institution it claims to be exposing, the simplest explanation is not that the institution lost control. The simplest explanation is that the institution never lost control at all.
THE NEXT PHASE
This piece will generate a response. We know this because we have documented what happens to people who publicly challenge this narrative. We have watched it happen to Red Panda Koala, to Tupacabra, to Beverly Holmes, to Jeremy McGowan, to Area 503 Manny, to Garry Voorhis, to Jon Simas, to Jay Anderson, to Ken Klippenstein, to Steven Greenstreet, to John Greenwald, to Kelly Chase.
We are prepared.
The Sentinel Network has filed this report with full awareness of the operational environment. Our sources are secured. Our evidence is preserved in multiple locations. Our network is decentralized. Our publication infrastructure is designed to survive suppression. And we may have set a few traps.
To the individuals within the Elizondo network who may be reading this: we are not interested in your personal beliefs about non-human intelligence. We are interested in documented patterns of behavior. If you have been a participant in or a witness to the proxy harassment operations described in this piece, and you want to set the record straight, we are reachable through secure channels.
To the experiencers who may feel attacked by this reporting: your experiences are your own and we do not question them. What we question is whether those experiences have been leveraged by people who do not have your best interests at heart. If someone validated your encounter and then pointed you at a target, you are not the villain of this story. You are a victim of it. Reach out. We want to hear from you.
To the members of Congress reading this who have been briefed in classified settings by individuals described in this report: you were briefed by a current government contractor. Ask yourselves whether the information you received was disclosure or whether it was a presentation. Ask who benefits from the policy outcomes you are being asked to support. Ask why the man urging you to grant amnesty to defense contractors is being paid by the Department of Defense. Ask why they don’t want this publication writing about a “comet”.
We will continue this investigation and have multiple briefings lined up. The financial records are being pulled. The pattern is documented. The network has been infiltrated. The sources are talking.
We don’t stop.
The disclosure machine is built on one assumption: that you will never look at who built it. You just did.
Keep looking up.
-- The Sentinel
Every briefing we’ve published is free. That’s not changing. This publication has no institutional backing, no sponsors, and no editorial board. We’re doing the work the newsrooms won’t — sourcing papers, filing FOIAs, building tools, and writing at the pace a once-in-a-civilization event demands.
Paid subscribers fund the investigation directly. They also get access to the comment section on every briefing, Fieldcraft Labs, and the FIELDCRAFT series — the tools and methods behind every investigation we publish. No ads. No sponsors. No strings. Your subscription is a data point against the suppression gradient.
If you can’t subscribe, we don’t care. Read everything. Share everything. The mission is the mission.
Subscribe to The Sentinel Network
Share this briefing. You have just seen what happens when this coverage reaches platforms that don’t want you reading it. Every share, every restack, every forwarded link is a data point against the gradient.
Previous briefings: THE BLIND SPOT | THE PHONE GAP | THE LONG COUNT | THE GREEN BURIAL | THE GHOST GENERAL | THE DEAD DROP | THE NARROW BAND | THE VERDICT | THE OPERATING SYSTEM



Absolutely amazing work. I’m grateful for your journalism. I will do my best to get more paid subscribers for you. Please take a look at the Secrets of Skinwalker Ranch next. Always known the show only shows what’s allowed, but never asked the question of how it connects to the DoD and why Bigelow’s time is classified with the same team making guest appearances on the show.
I have wanted to believe that Lue Elizondo was making a good faith effort at public advocacy for disclosure but your investigation has given me some additional serious doubts that I can continue to trust that is true. But I can't honestly say that I care all that much about motivations, i.e., your statement "The question is whether the people telling you about UFOs are telling you the truth about why they are telling you." I'll be 72 in June. Before I die, I minimally want an official statement from my government that an alien craft crash landed and was subsequently recovered as well as some presentation of evidence of same. Whether I get that official statement and evidence as the result of good faith public advocacy or as a result of a limited hang out is a very distant secondary concern. I care very much whether Elizondo is telling the truth about the phenomenon but why he is telling me barely registers as concern in comparison. Yes, he hammers the threat narrative/interpretation, as the saying goes, to a hammer every problem is a nail. One of his prior jobs entailed threat assessments and there is a credible case to be made that we are and have been under surveillance by forces unknown. And it's obvious the national security angle is a good way to motivate Congress to act on legislation, either he or Mellon have stated as much. The most troubling inference of your investigation to me, is that Elizondo may have used vulnerable personalities to harass others who have been critical of him. If true, that's reprehensible.